Security is the key aspect while developing web applications, especially when data deals with confidential information. Full fledge secure web applications must capable of protecting the data. The team has to identify the potential risk and vulnerabilities initially at the requirement Security is critical when developing web applications, especially when dealing with sensitive data. Full-fledged secure web applications must be capable of data protection. During the requirement phase, the team must identify potential risks and vulnerabilities. Having strong security practices has an impact on brand value; otherwise, it will result in revenue and customer loss. The government is getting stricter with businesses that don’t adhere to adequate security requirements, which can lead to costly fines, penalties, and legal action. Learn some tips on how to secure applications from vulnerability attacks.
In this post, we’ll go over some security checklists for web applications in order to protect them from malicious and vulnerable attacks.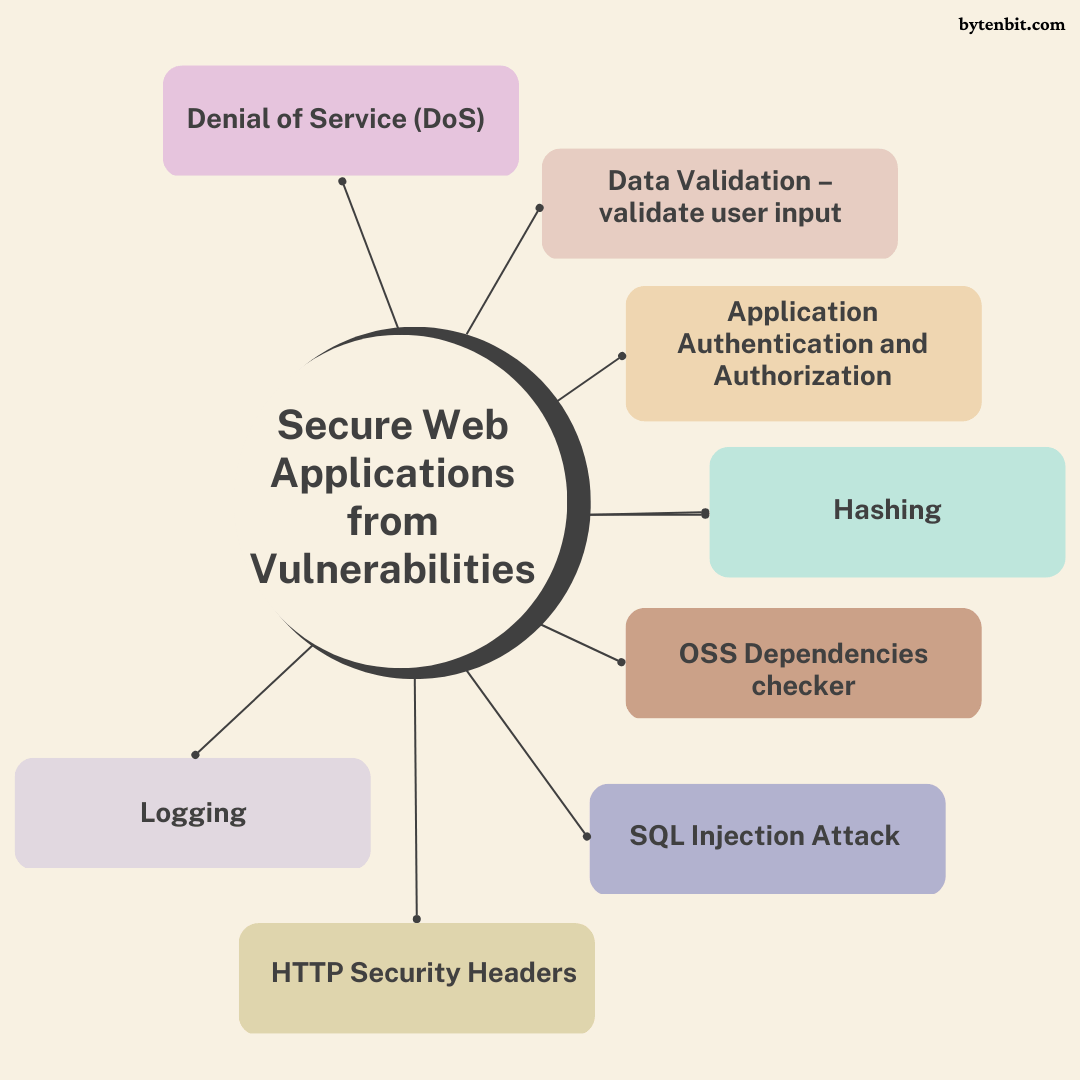
Data Validation – validate user input
Always sanitize data. Any input from the user should be treated as untrusted data. Having no validation at the application and database level, there is a potential risk that causes security to exploit the issue. however, this ensures data in the database should be in a clean and valid format.
External libraries are used to validate the input data. It can be used in your next Node or Go project.
- joi – Powerful data validation library for JS Node JS.
- validator – Validations for structs and individual fields.
Application Authentication and Authorization
Authentication includes verifying users before serving a request. This helps us to restrict an unauthorized persons to access data. To prevent this vulnerability. In order to avoid this vulnerability. Before performing any operation, each request should be authenticated. For authentication, use industry standards such as JWT and Oauth2.
Authorization: The process of verifying a user’s permission is known as authorization. Applications have different roles that have specific permission to perform specific operations. The server returns data based on the user’s role. At the application level, proper role-based access control should be implemented. As a result, only an authorised individual has access to a specific resource. If data were to reach an unauthorised person, this would result in reputational harm and regulatory penalties from the government.
External libraries to achieve authentication and authorization for JS or Go projects.
- passport – Simple, unobtrusive authentication for Node.js.
- casbin – Authorization library that supports access control models like ACL, RBAC, ABAC in Golang.
Hashing
Golder rule: Never ever store confidential data like passwords and bank details in plain text version. Always generate the hash and sstore it in the appropriate database or files. Hashing is a function that generates a unique string that can be decrypted later. Many existing hashing algorithms already exist in the market which provides great support for hashing mechanisms. Password and confidential data should be hashed with one of the following algorithms BCrypt, SCrypt, MD-5, and SHA-3. Even if an attacker gains access to the database, they will not be able to extract the password or other sensitive information. Given that hashing is a one-way function.
External hashing library for JS or Go projects.
- bcrypt.js – Optimized BCrypt in plain JavaScript with zero dependencies.
- bcrypt – Implements BCrypt adaptive hashing algorithm in Go
OSS Dependencies checker
Open source software is popular among developers because it allows them to quickly implement new features and is completely free. However, it comes at the expense of vulnerability, and the code is easily accessible to anyone because it is open-source. Many third-party dependencies are used in projects today. Always ensure that dependencies are bug-free and active maintainers.
There are tools available on the market that can find vulnerabilities that have been made publicly available and give full information on any anomalies found, potential remedies, and more.
GitHub has already begun to examine our repository for potential vulnerabilities. To achieve the same thing in local repository one can use the following packages
SQL Injection Attack
SQL injection is a security vulnerability that allows an attacker to modify the application queries. It allows an attacker to access unauthorized data such as passwords, credit card details, or user information data. Even an attacker can create, update or delete data.
To prevent SQL injections, one should use escape the values when query values are variables provided by the user. Alternately, use third-party programmes to accomplish the same thing.
- sql-injection – Detects SQL injection attacks and stop them.
- gorm – Escape arguments to avoid SQL injection in Go.
HTTP Security Headers
HTTP security headers are part of HTTP headers that are exchanged between a client (typically a browser) and a server to specify the security of HTTP communication. By making security headers available in web applications. As a result, it safeguards applications against the most common attacks that your site is likely to face, such as cross-site scripting (XSS), code injection, and clickjacking. HTTP security headers add an extra layer of security by limiting the behaviors that the browser and server permit once the web application is running.
The Most common HTTP Security Headers are
- Strict-Transport-Security
- Content-Security-Policy
- X-Frame-Options
- Cache-Control
- X-frame-Options
- X-XSS-Protection
- Referrer-Policy
Netsparker wrote a great article about HTTP Security Headers. To verify security headers, visit securityheaders tool.
To enable security headers for your application you can use these packages which provide out-of-box functionality.
- helmet – secure your Express apps by setting various HTTP headers.
- secure – HTTP middleware for Go that facilitates some quick security wins.
Denial of Service (DoS)
A denial-of-service attack is a cyber-attack that prevents other users from accessing a resource, causing it to crash or become unavailable. This is accomplished by flooding the server with a large number of requests, which causes the CPU memory usage to increase and the system to crash. The DoS attack is a vulnerability that is exploited to bring the system down.
Few techniques to prevent DoS attacks.
- Rate limiting – limit the number of requests from the users. If more request comes from individual user block those users.
- Google reCAPTCHA – protects the server from fraud detection service that stops bots and other automated attacks while approving human.
- Monitor traffic – Background checks which analyze the request. If some uncertain activity is found at usage then block the IP’s or user’s account.
Open-source tools that help to prevent Denial of Service attacks.
- express-rate-limit – About Basic rate-limiting middleware for express.
- ratelimit – A Golang blocking leaky-bucket rate limit implementation.
Logging
Applications log contains information about events that occurred in applications. These logs are written to the file. Logging helps to identify details about requests, inputs, login, IP address, security headers, errors, and warnings. Having application logs helps us to debug bugs and monitor the health of the applications. Programmers can learn about how the vulnerability occurs within the system with the help of the application logs. Later can restore the application with data correctness. Even though the attack is unsuccessful by an attacker, the Programmers have all the logs of what technique the attacker is trying.
Note: Make certain that no sensitive or confidential information is logged in the logs.
To capture these details in your NodeJS and Go application. One can use these open-source tools
- winston – A logger for just about everything.
- go-logging – Golang logging library
Applications should be well-protected against potential security threats and vulnerabilities. And a daily monitoring check must be performed. These are the few practices that help us to secure applications.
- Accept complex passwords that are both long and strong. A short password is vulnerable and easy to brute force.
- Web applications should use an SSL certificate. And Redirect All HTTP Traffic to HTTPS.
- Use extensive quality assurance and testing.
- Keep web apps up to date and use the latest dependency safely.
- Organize security awareness training for your teams and introduce bounty program.
- Be careful while generating authentication tokens and have a short expiry time.
Also, visit:
- Easiest Way To Embed Newest Facebook Post into Website Automatically
- Google Gmail Labs – Effective Way To Enhance Email Productivity
- Embed an Image from Google photos into your Website
I’d like to know what approaches you’re taking in your project to develop secure applications from vulnerability attacks. Please share in the comments section.





